This spring, during VeeamON 2017, Veeam Software presented Veeam Powered Network (VeeamPN), their first solution in the field of enterprise networking.
Here is its brief video review by Anthony Spiteri, Veeam evangelist:
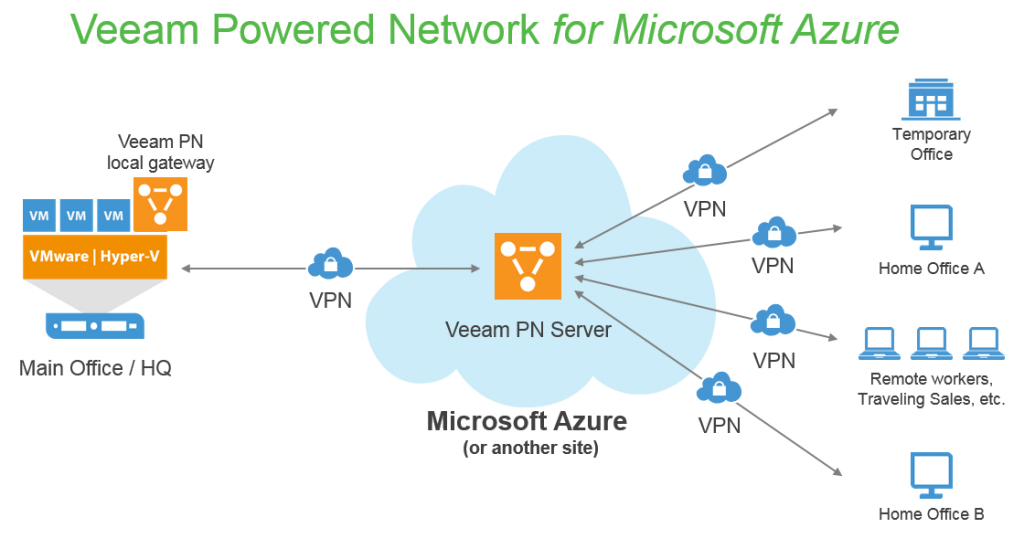
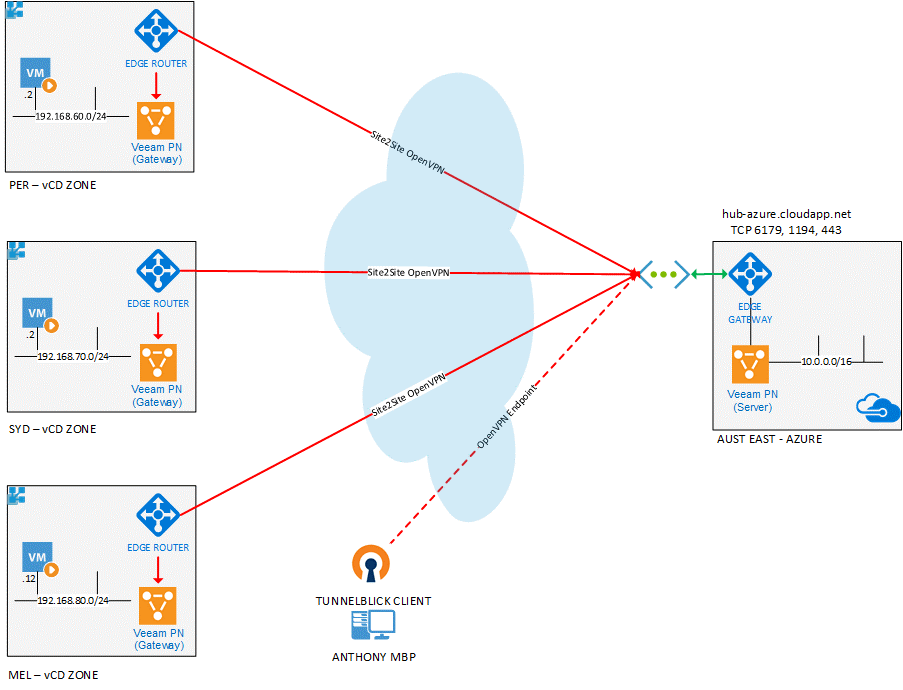
Veeam PN is a simple tool for establishing VPN between all parts of a distributed infrastructure: the headquarters, remote and branch offices, employees working remotely, etc. This solution is based on the OpenVPN technology. It serves as a virtual machine, running in Microsoft Azure (Veeam PN Server) or client’s private cloud, with the components on customer’s sites (Veeam PN Gateway):
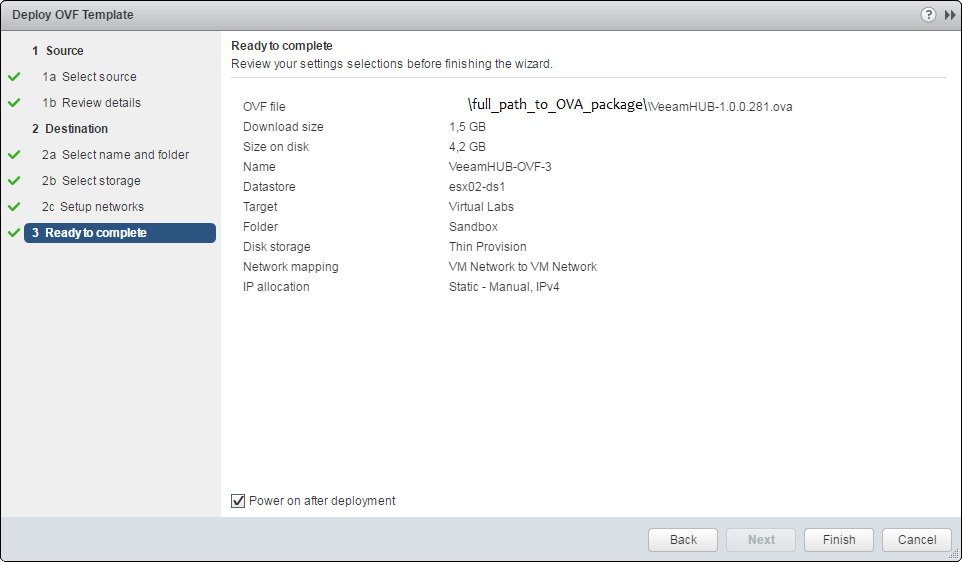
In addition to Azure-based Veeam PN, any VMware vSphere on-premises VM environment may serve as a central routing server. For this purpose, it is necessary to upload and deploy a virtual Veeam PN Appliance module as an OVA file.
It should be noted that Veeam PN is a completely free product that serves as a network basis for Veeam Recovery to Microsoft Azure, a complex solution for ensuring datacenters’ disaster resiliency. Veeam PN can be also used as a VPN for companies seeking for an easily-scalable virtual private-network infrastructure.
Veeam PN network infrastructure may have any configuration. For example, it may be an environment with a Veeam PN Server virtual machine in Azure, Veeam PN Gateway client’s software in three geographically separated datacenters, or even external private network users connecting via OpenVPN Client.
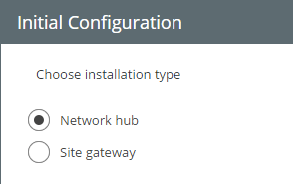
During product’s deployment, you should specify one of the following options:
- Network Hub is a Veeam PN server deployed in Azure or in the private infrastructure.
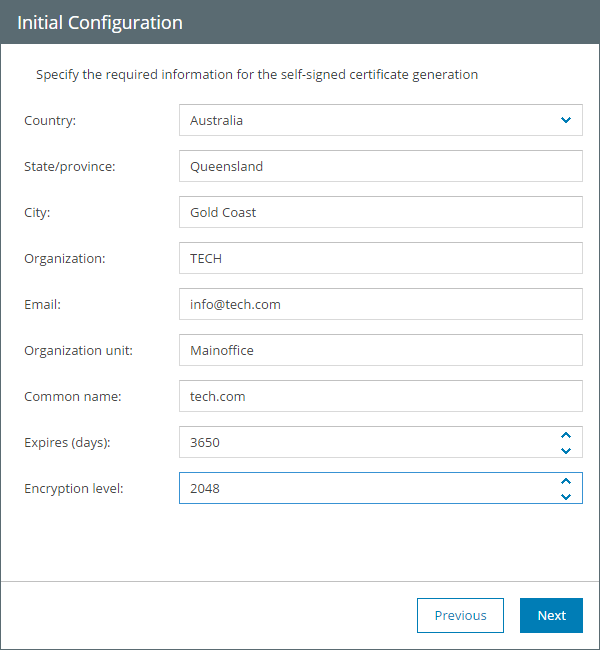
- Site gateway is a virtual machine serving as a gateway for Veeam PN with 2048-bit self-signed certificates for communication.
The initial setup is described in the image below:
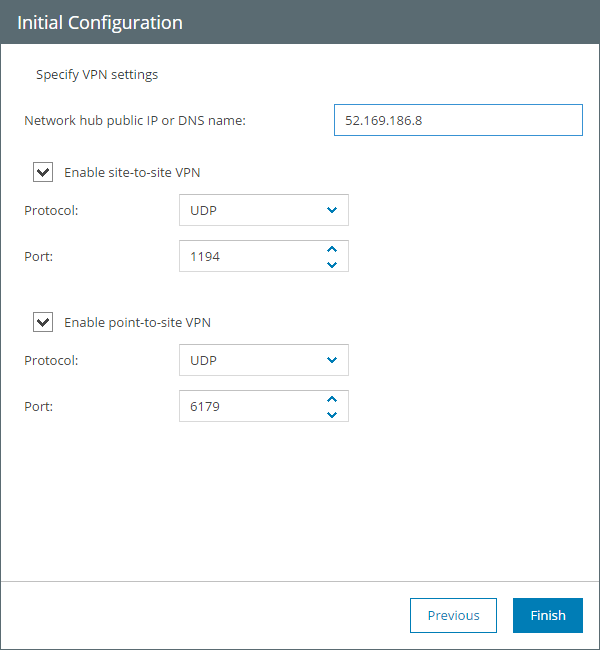
Further, we set up network communication properties:
- Network hub public IP or DNS name determines a public address that all members of the private network can access (including the remote clients outside the private cloud).
- Enable site-to-site VPN option should be checked if communication between datacenters (Veeam PN Gateways) is needed.
- Enable point-to-site VPN allows communication between OpenVPN Client and a Veeam PN Gateway component on datacenter’s site.
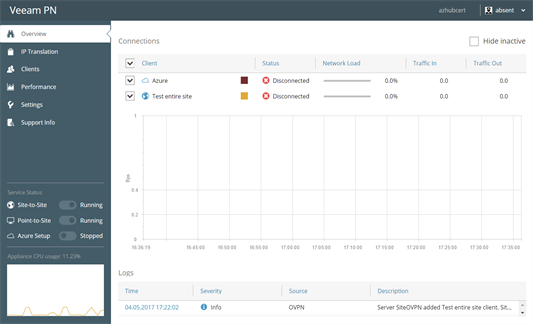
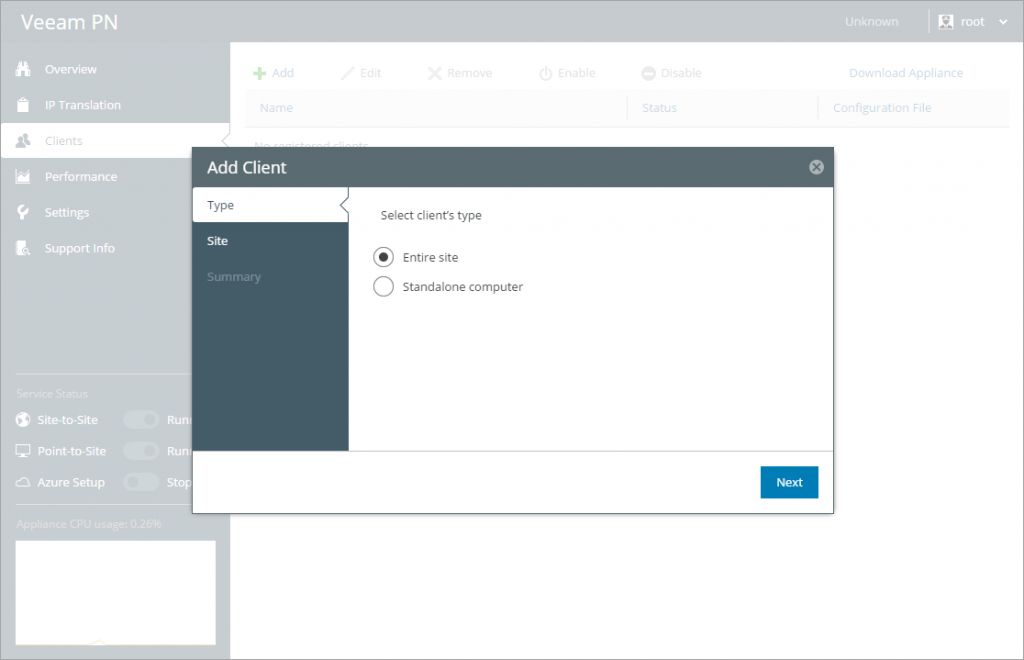
Once Veeam PN Server is deployed, we need to generate settings file for datacenter networks (a site-to-site scenario) and standalone computers (a point-to-site scenario). For this purpose, computers and sites must be registered on Veeam PN Server (Hub portal):
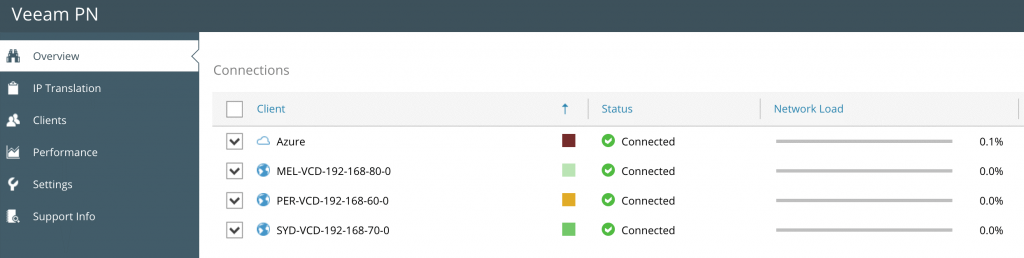
As a result, we get the list of registered sites and separate clients:
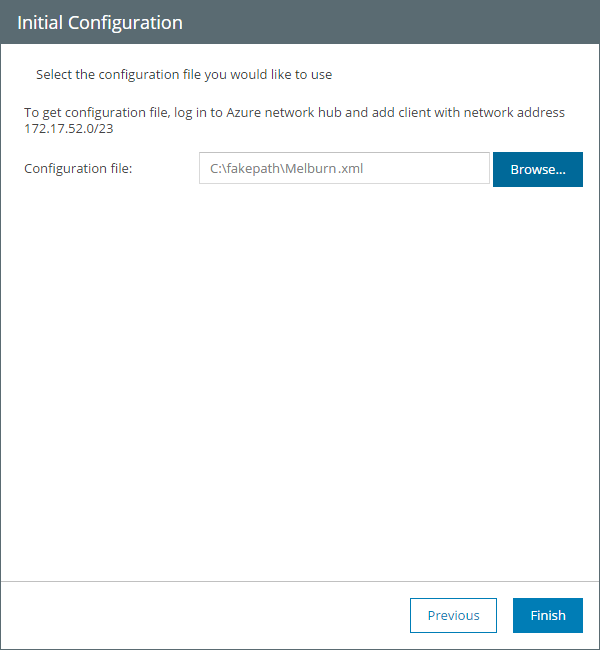
Once clients are registered, VPN settings for clients and sites should be downloaded as an XML file. These settings must be imported during Site Gateway deployment:
If Network Hub Server is deployed in the on-premise network, the new route in the Default gateway is to be added to the network with Veeam PN Server. The route should be also added to the sites’ networks with Site Gateway to make both sides of the VPN tunnel aware of the new route. You can find more information here.
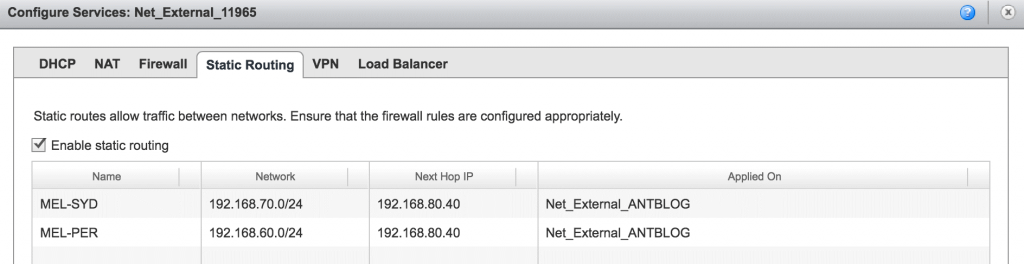
When you register Site Gateways on the Network Hub site, and upload its XML configuration file on the site, you allow the gateways to find out Network Hub location and zones that Site Gateways are responsible for. Virtual machines running on the sites need to be able to access VMs in other zones through default gateways. That, actually, is why the static routes are to be added. Once data passes Site Gateway and reaches the Network Hub, it is redirected properly to the corresponding site through its Site Gateway.
For instance, you may have the following infrastructure (the example can be found here):
The table of static routes on MEL site will look like this:
Here, Site Gateway of this site serves as Next Hope. Further, Site Gateway sends the traffic to Veeam PN Server. Afterwards, the data is sent to another machine on different site. The route is the same for other sites.
If Veeam PN Server is used in Azure, it is not necessary to add new routes because Veeam PN automatically adds the necessary routes in routing tables. Besides, infrastructures on premises of different public cloud services (laaS, AWS, IBM, Google, etc.) can be used as a component of Veeam PN network infrastructure.
Free Veeam PN solution can be downloaded here. Veeam Recovery to Microsoft Azure trial version also can be downloaded via the link above.