In my previous blog post we looked at the process of configuring screen sharing in Ubuntu 18.04.02 and connecting to Ubuntu desktop using VNC Viewer client. That can be something useful for remote assistance or for other scenarios where it is OK for you to open local session first and connect to it using VNC Viewer afterwards. Back then I was interested in that to enable copy paste into Ubuntu session running in a Hyper-V VM on my laptop, but by the time I finished that article Hyper-V Quick Create Ubuntu images were made available, which have xrdp configuration allowing use of Hyper-V extended session with working copy-paste between Hyper-V host and guest VM, so if all you need is copy-paste for local Hyper-V Ubuntu VM you can stick with Ubuntu images from Hyper-V Quick Create gallery. For other scenarios where you want to be able to connect to Ubuntu machine using some sort of remote desktop client without need to open session locally you will need to install and configure some remote desktop server on your Ubuntu machine.
There are different protocols and implementations of remote desktop GUI servers based on those, most notably Microsoft Remote Desktop Protocol (RDP) and Remote Frame Buffer protocol (RFB), as well as such protocols as X Window and SPICE (Simple Protocol for Independent Computing Environments). In addition to the protocols per se, wide variety of remote desktop servers based on these protocols is available for Ubuntu, and each of those implementations has its own strengths and weaknesses.
In this post we will look only at XRDP server, open source implementation of RDP server. XRDP is compatible with Gnome 3 shell which replaced Unity shell used by default in Ubuntu prior to version 17.10. Gnome 3 is what you have by default in desktop version of recent builds of Ubuntu operating system. In case you are not sure which shell you are using you can confirm it using wmctrl -m command (you may need to install wmctrl first using sudo apt install -y wmctrl first):
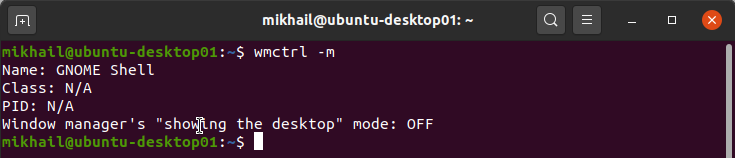
Checking which shell/window manager you are using with wmcrtl command
Unity shell used by older, pre 17.10 versions of Ubuntu and it had some issues in terms of using it with XRDP. We will be going through all the configuration steps using Ubuntu Desktop 20.04 image which includes Gnome 3 version 3.36 by default. You may check installed Gnome version using gnome-shell –version command as shown below:
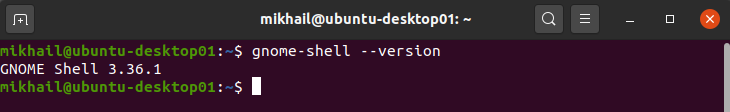
Checking Gnome shell version with gnome-shell –version command
In case you don’t have Gnome 3 shell installed you can do that using sudo apt install -y gnome-session gdm3 command (it takes around 15-20 minutes to complete depending on your internet connection speed among the other things).
Once we made sure we have Ubuntu with Gnome shell installed, we can proceed with XRDP server installation. Being free and open-source implementation of Microsoft RDP server, XRDP allows to connect to it using standard Windows RDP clients which simplifies life for anyone connecting to it from Windows based workstations which have necessary client software available out of the box.
As usual we start with updating APT package index to made APT aware about the latest available package versions using sudo apt update command:
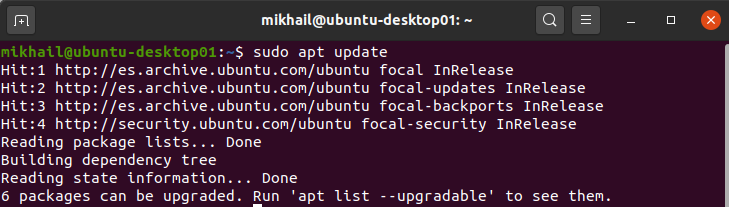
Updating APT package index
Next, we should install XRPD server using sudo apt install -y xrdp command:
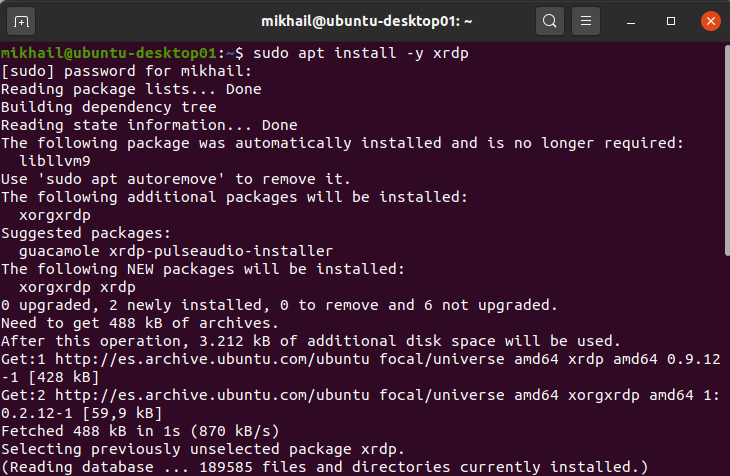
Installing xrdp server package using APT
Once XRPD package has been installed XRPD server starts automatically and you can check its status using sudo systemctl status xrdp command:
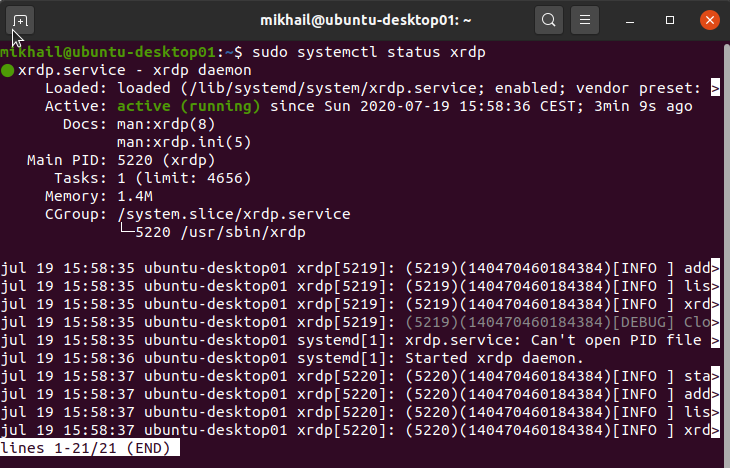
Checking XRDP server status
To enable XRDP service at a system boot time we need to use sudo systemctl enable xrdp command as shown below:
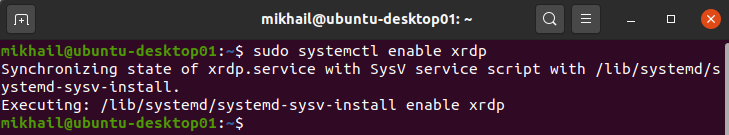
Enabling XRDP service to start on system startup
At this point you can reboot your Ubuntu machine (using either sudo reboot command or GUI to initiate reboot) and try to connect to it from Windows workstation using MSTSC client. For that you just fire off mstsc.exe from Run menu and after typing in your Ubuntu machine name hit Connect button. After standard MSTSC security warning asking you to confirm that you want to connect to this computer will be presented with XRDP login prompt within MSTSC window as shown below:
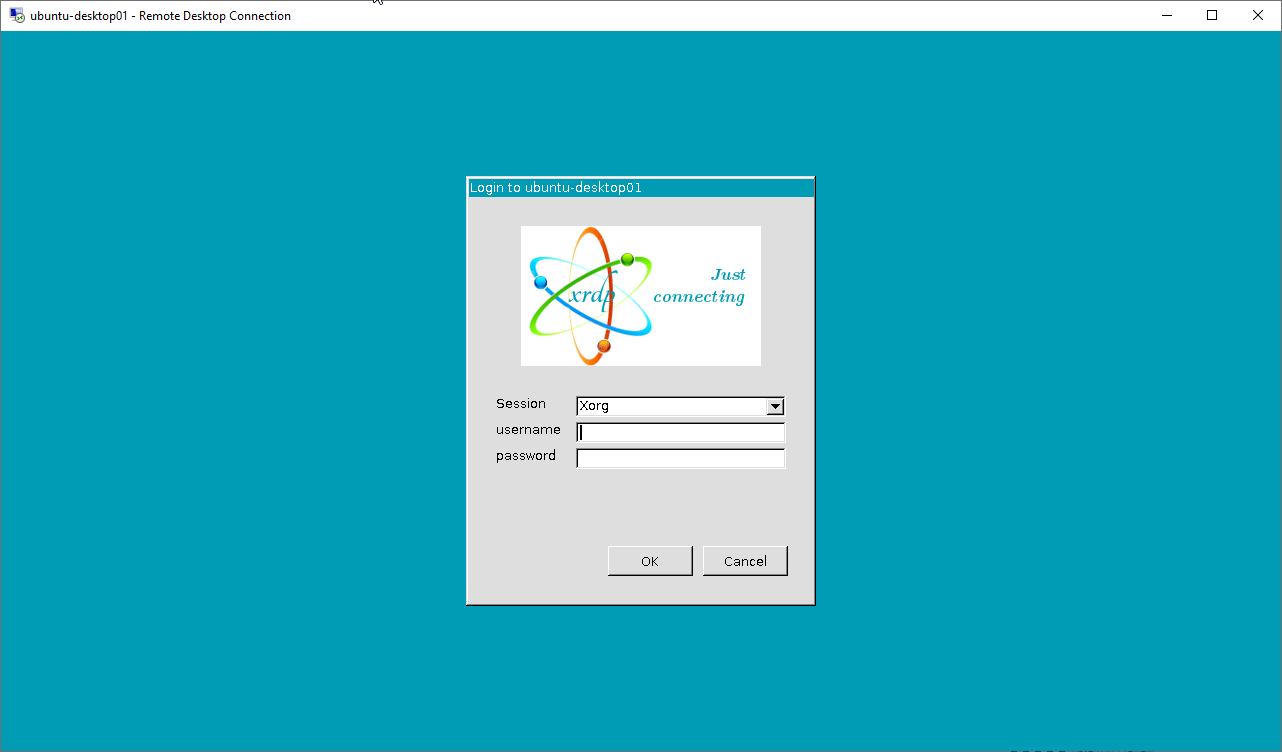
XRDP login prompt
If you reached this stage it confirms that XRDP installation and configuration went well and XRDP server starts at machine start up. Now, once you type in the correct username and password you will see another authentication prompt from Ubuntu requiring you to type in your Ubuntu password once again saying “Authentication is required to create a color managed device”:
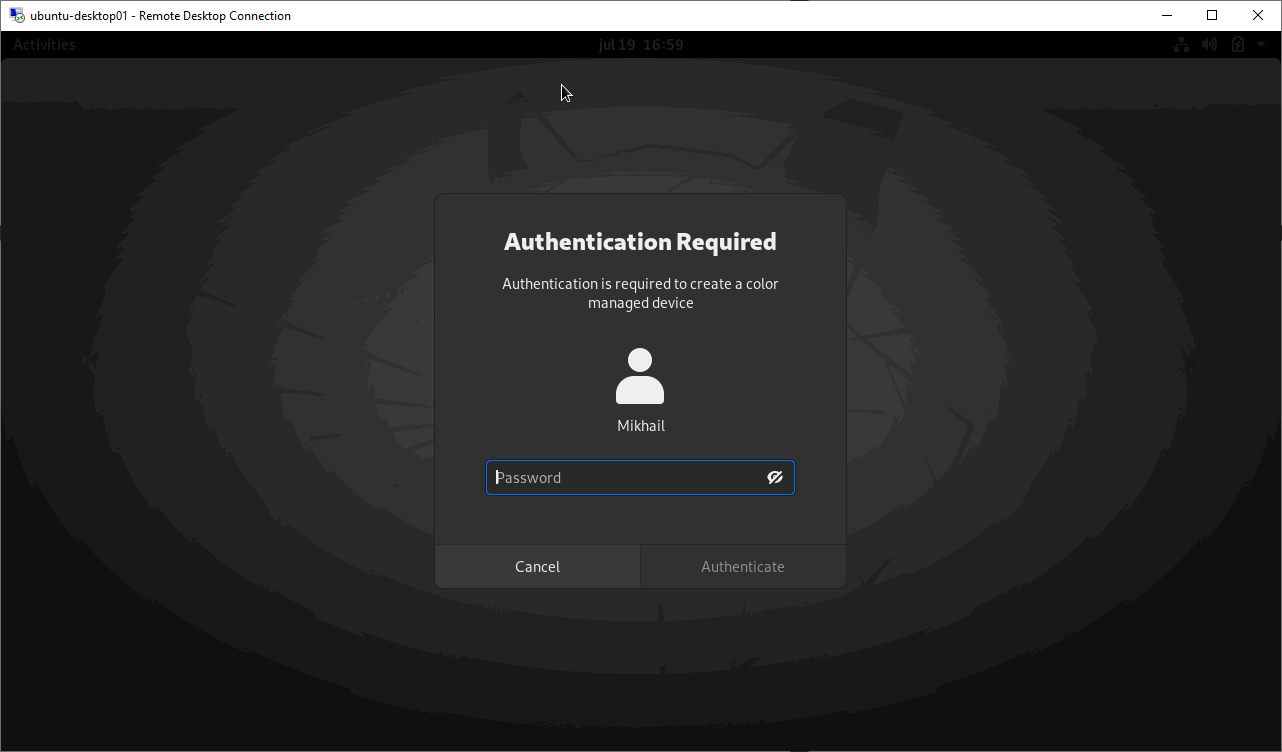
Authentication Required to create a color managed device
Once you type in your password for the second time there you will be presented with fully operational Ubuntu desktop remote session as shown below:
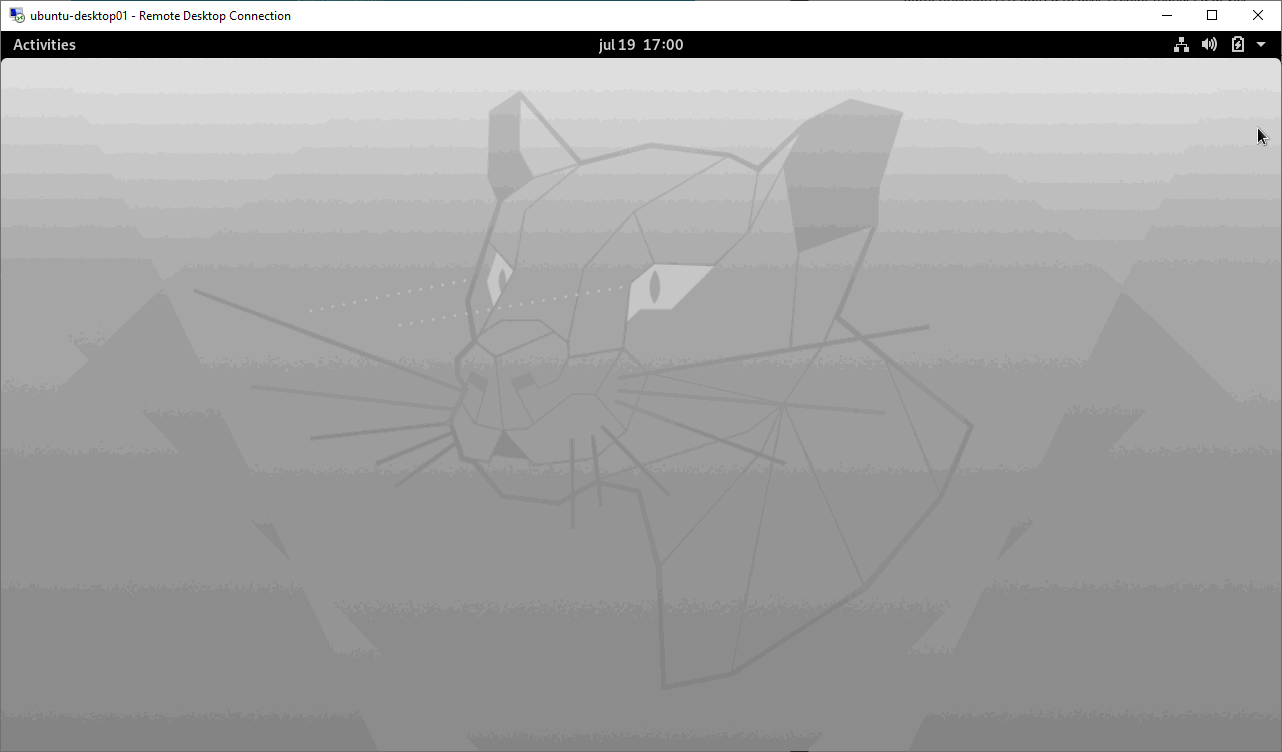
Ubuntu GUI presented through RDP session
Now we can look at the couple of extra things you may want to adjust. As you have seen when connected to XRDP server session we are getting extra authentication prompt and you might have noticed that Gnome Desktop Dock is minimized requiring you to click on Activities to make it visible which is not inline with default Gnome shell experience you get when connecting through local connection. Let’s address those two things.
First let’s deal with “Authentication is required to create a color managed device” password prompt. It comes from Polkit policy. Polkit, formerly knowns as PolicyKit is a component for controlling system-wide privileges in Unix-like operating systems used in Ubuntu. Ubuntu 20.04 uses Polkit version 0.105 and you can verify this using pkaction –version command as shown below:
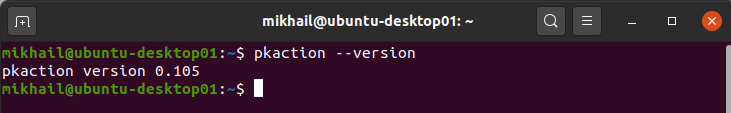
In case of Polkit 0.105 to get rid of this authentication prompt we should add custom Polkit rule creating xrdp-color-manager.pkla file using sudo nano /etc/polkit-1/localauthority/50-local.d/45-allow-colord.pkla command and add the following content into it:
|
1 2 3 4 5 6 7 8 9 10 11 |
[Allow Colord all Users] Identity=unix-user:* Action=org.freedesktop.color-manager.create-device;org.freedesktop.color-manager.create-profile;org.freedesktop.color-manager.delete-device;org.freedesktop.color-manager.delete-profile;org.freedesktop.color-manager.modify-device;org.freedesktop.color-manager.modify-profile ResultAny=no ResultInactive=no ResultActive=yes |
Note that what you see between ” Identity=unix-user:*” and ” ResultAny=no” should be typed as a single line of text in that file. Here is how your 45-allow-colord.pkla file should look like in nano editor:
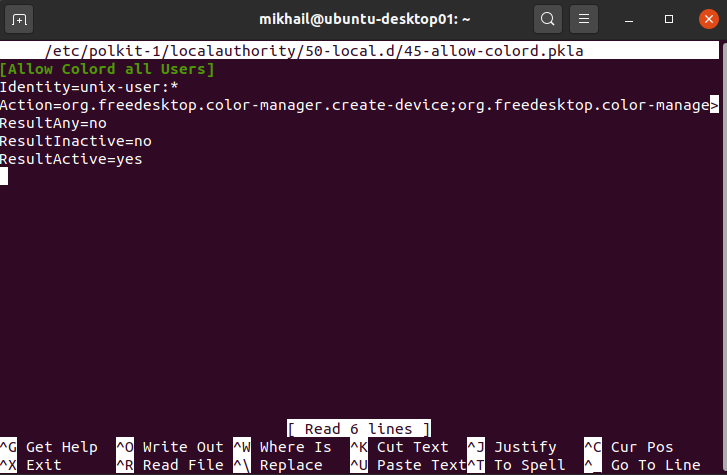
Contents of 45-allow-colord.pkla file
Note that this policy configuration is specific to Polkit version and if you have Polkit 0.106 or newer this configuration will cause “System program problem detected” pop up, as newer version requires different configuration settings for this scenario.
Now let’s have a look at hidden Gnome Desktop Dock issue. To address that we can install Gnome Tweaks tool using sudo apt install -y gnome-tweak-tool command:
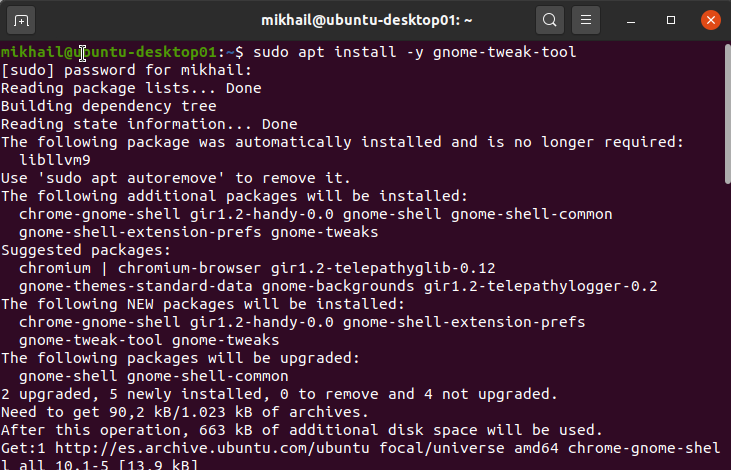
Installing Gnome Tweaks tool package
Once it installed, we need to open Tweaks tool and enable Ubuntu appindicators and Ubuntu dock under Extensions as shown below:
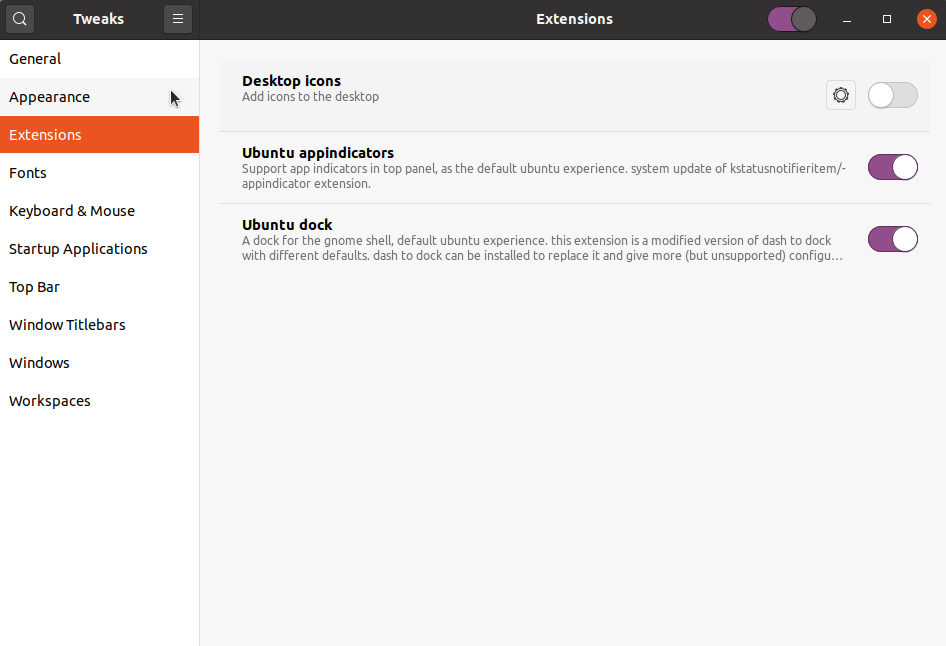
Enabling Ubuntu appindicators and Ubuntu dock in Tweaks tool
With these settings in place your remote Ubuntu session will have dock always visible the same way as you have it when connecting to local session:
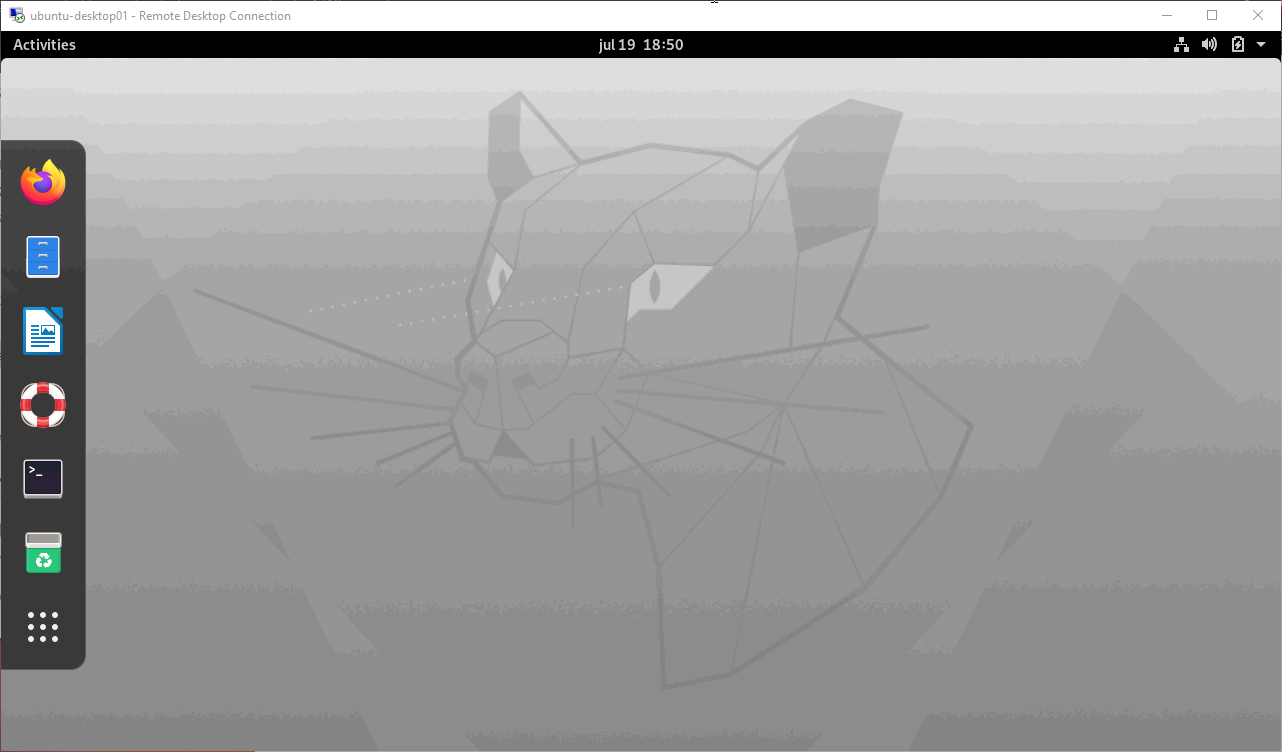
Ubuntu XRDP session with dock visible
Last but not least you may want to configure your Ubuntu firewall to allow RDP connection only from specific subnet or IP address which will be a good idea when your Ubuntu machine exposed to Internet. When you perform Ubuntu Desktop installation from default image and with default settings your firewall is not enabled, which you can confirm with sudo ufw status command:
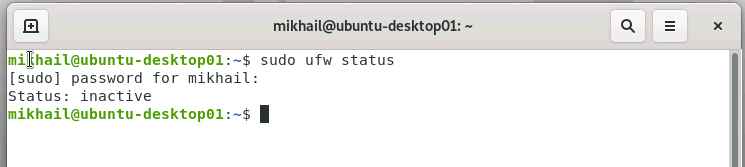
Checking ufw status
Let’s create RDP connection rule making sure we access from subnet or IP of our RDP client(s). RDP protocol uses port 3389 by default and example below creates a rule allowing access through this port from subnet 192.168.1.0/24:
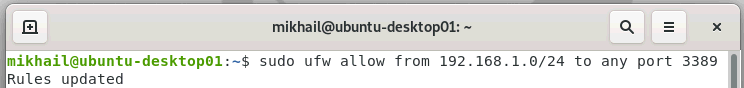
Creating ufw rule for XRDP access over port 3389
Once we created firewall rule with sudo ufw allow from 192.168.1.0/24 to any port 3389 command, let’s enable firewall and check its status again using sudo ufw enable and sudo ufw status commands respectively:
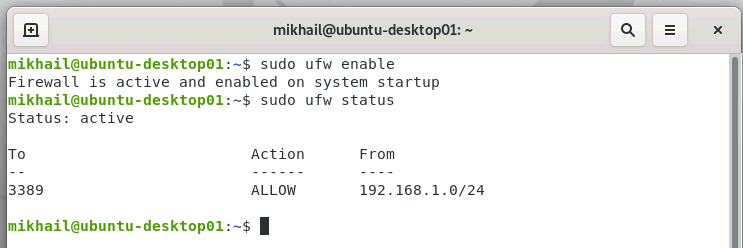
Enabling ufw and verifying its status
In case of sensitive / real-world servers and desktops you would want to take care about your firewall configuration before installing and enabling XRDP, but this article was written on assumption that you just learning how to do it using dummy test machine which contain no sensitive data. Of course if your Ubuntu VM is hosted in some sort of cloud there can be other firewalls or security controls which you will need to configure to allow RDP access on a network level but covering this falls out of scope for this introductory level article. In case you want to dive in into XRDP security settings looking at options available in /etc/xrdp/xrdp.ini file can be a good starting point.
That concludes our little XRDP configuration walkthrough. In this blog post we looked at the process of installation and configuration of XRDP server on Ubuntu 20.04 desktop machine in order to be able to connect to its graphical shell (Gnome) over the network using standard Windows RDP client (aka MSTSC). I hope this post has been informative for you and helped to get you started with XRDP server and Ubuntu remote access configuration. Feel free to leave your questions and feedback in the comments section below.




