If you’ve been talking to customers about a cloud, no matter what platform, I’m pretty sure that you heard from almost any of them that one of their major concerns about the public cloud paradigm is security. Especially when you are talking to the public sector or private companies, like financial institutions, where their entire business relies on their workloads and users secure environment.
Azure Government represents an isolated version of Azure dedicated to these customers, where most of the Azure features are available under strict compliance rules. In order to enhance this service, Microsoft released recently to GA (General Availability) a key component of the Azure Government service: Virtual Cloud Defense (VCD).
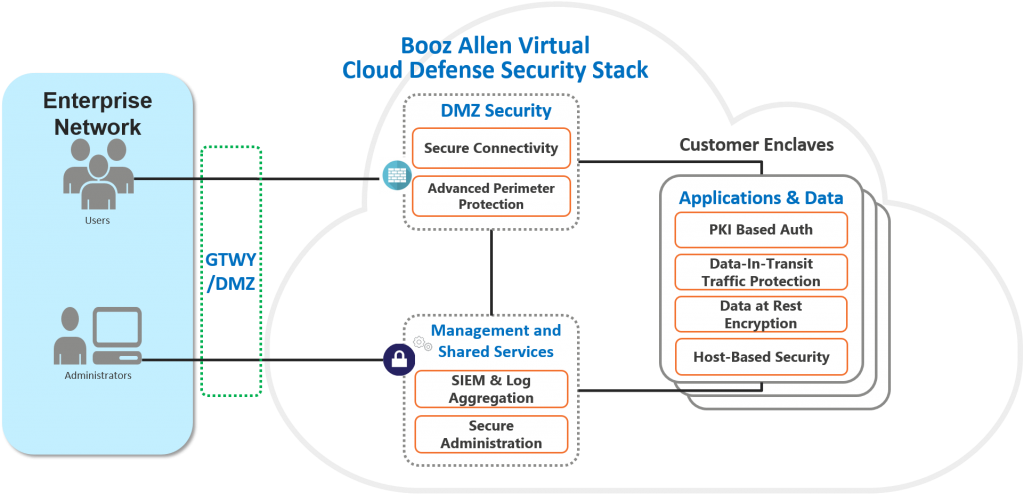
This initiative led by Microsoft and Booz Allen (the company based in Virginia with a strong focus on security within technology) and introduces several enhancements to the Azure Government platform and their customers. Some of the most important ones:
- Encryption of Data at Rest: with native Azure and third-party solutions that offer encryption of cloud storage, data is protected from unintentional disclosure and malicious activity
- Network Traffic Inspection and Protection: in-line packet inspection and passive SSL decryption of traffic into and out of Azure Government, as well as between Azure virtual machines and virtual networks, detects and blocks intrusions and other malicious traffic
- Log Aggregation, Dashboards, and Analytics: the collection and analysis of security events and configurations range from network appliances, cloud infrastructure, operating systems, and applications to support security operations, auditing, and executive reporting
- Identity and Authentication Services: integration of these services with Public Key Infrastructure (PKI) supports Common Access Card (CAC) and multi-factor authentication for hosted applications and management functions
- Network Tiering: a framework for restricting traffic between zones, based on user-defined criteria, VCD’s network tiering provides logical network segregation of security zones, user planes, data planes, and management planes
- Deployment Automation: Azure Resource Manager expedites initial setup and configuration.
Virtual Cloud Defense (VCD) is basically providing an additional set of features and umbrella under Azure Government. Under the VCD umbrella, customers can maintain their workloads secure, while integrating them with 3rd party components, securing the communications between them, providing analytics information and other important aspects.
A Little Bit More about Azure Government
In order to guarantee their customers about the compliance level you can achieve within Azure Government, Microsoft applied for the highest authorization level and security audits available.
Some of these specific security standards are SO/IEC 27001 and ISO/IEC 27018, FedRAMP, and SOC 1 and SOC 2. You can access the Microsoft Trust Center / Compliance portal where you can obtain information about each of the cloud products, including Azure Government.
Here’s the list of regulations and standard fulfilled by Azure Government:
As you can imagine, all these badges come with some restrictions and differences about the Azure environment we commonly known. Therefore, Microsoft stated some disclaimers when you start looking into Azure government:
- There are services and feature differences, this means that certain features that are in specific regions of the Global Service may not be available in Azure Government.
- For features that are offered in Azure Government, there are configuration differences from the Global Service. Therefore, you should review your sample code, configurations, and steps to ensure that you are building and executing within the Azure Government Cloud Services environment.
- You should refer to the Azure Government Technical services documentation for information that identifies the Azure Government boundary and customer regulated/controlled data guidance and best practices.
“I reviewed the disclaimers and I know that Azure Government is the right platform for me and/or my customers, how much is going to cost me?” There’s an easy answer to that as well: Microsoft released in September the Azure Government Pricing Calculator.
Consumers will now be able to calculate and estimate the cost of using Azure Government services by selecting one of the two “US Gov” regions.
In case you were wondering, Amazon also has their own Government edition of their cloud: AWS GovCloud (US).
- Veeam + StarWind: Security for Mission-Critical Data
- Azure Offers Backing Up VMware VMs with a Freeware Tool